Experience the
Difference
AMD has saved clients millions of dollars in IT costs, but we can do more than that for your business.
Connecting Your Business to Top
Technology
AMD has relationships with leading telecom and cloud providers to solve real business problems.
Contact our Corporate Sales team:
1-603-932-7388
The Perfect
Providers
Real business problems require real business solutions. AMD works with an arsenal of trusted, carefully vetted service providers, ranging from traditional and niche telecom to cloud services. With access to the latest technologies across a wide range of carriers, AMD can help your organization tackle a broad range of business issues.
Making Your Business
a Priority
With AMD as your trusted technology advisor, our loyalty and commitment to you always comes first. Interested in learning more? Contact us today.
AMDTechnology
AMD Technology’s history is a testament to relentless innovation and groundbreaking advancements that have revolutionized the world of computing.
AMD Technology empowers businesses to maximize their return on investment by delivering high-performance computing solutions that enhance productivity, efficiency, and profitability.
AMD Technology’s ultimate goal is to drive technological innovation forward, empowering businesses and individuals alike to unlock their full potential and shape a better future through groundbreaking computing solutions.
AMD Technology proudly serves an exceptional clientele of global industry leaders, empowering their success through cutting-edge computing solutions and unparalleled performance.
Our Service Providers
Below is a partial list of domestic and global providers with whom we closely work to bring completely optimized solutions to your business:



“
AMD Technology has completely transformed the way we operate our business – their powerful computing solutions have significantly boosted our productivity and efficiency, while their outstanding customer support ensures a seamless experience. We can confidently say that choosing AMD Technology was the best decision we made for our company’s growth.
KATIE H.
BUSINESS OWNER

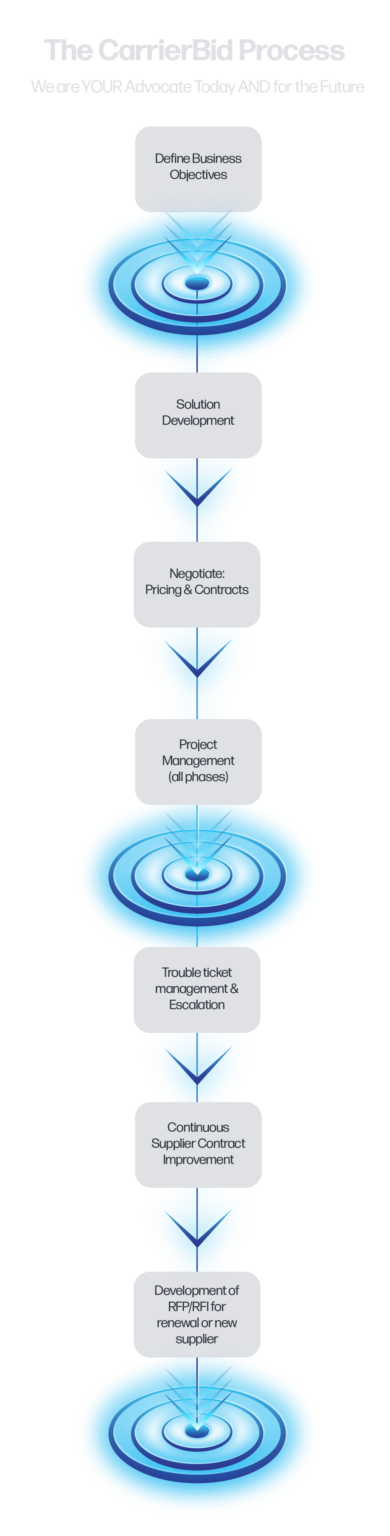
How it Works
1.
2.
3.
4.
Suppliers
Saved for Customers
Customers
Countries
STREAMLINE. CONNECT. ENHANCE. with AMD Technology
Join Our Newsletter
Only resourceful information. No spam, that’s a promise.
Get Started & Start
Saving
The average company is overspending by 20 – 40%. Is yours? Get a free quote and find out how we can optimize your technology and reduce costs.